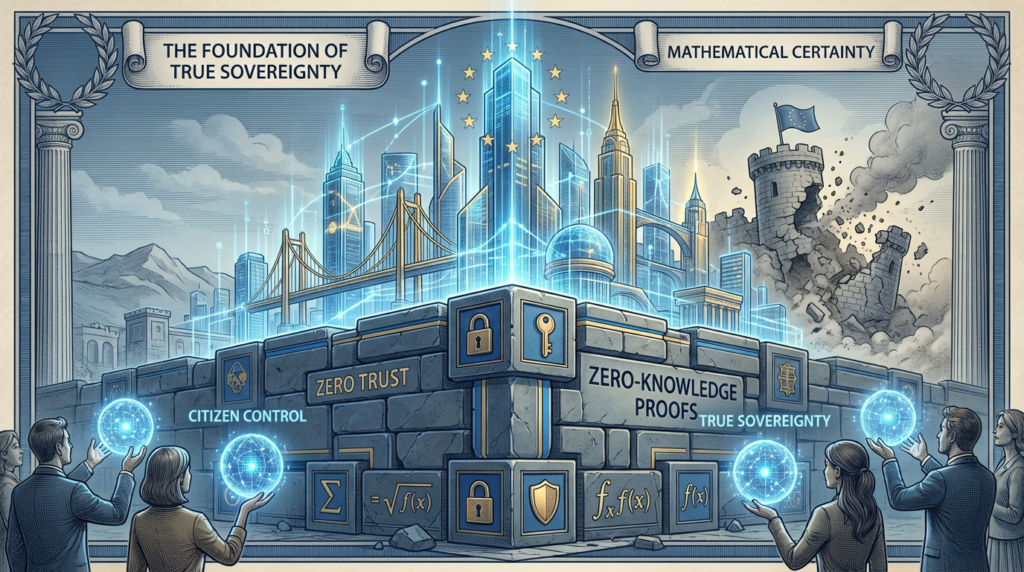
Sub-headline: Sovereignty Without Freedom Is Just Bureaucracy: Build a Digital Republic of Individuals. If “sovereignty” means more centralized control, you didn’t save Europe. True freedom requires optimizing security, decentralization, and a partner who can build resilient systems.
The Individual is the Smallest Minority
The quest for “digital sovereignty” is fraught with peril. If the end result is a larger bureaucracy, we have not achieved freedom. True sovereignty begins with the individual. In the digital age, this means building an infrastructure of freedom. As a professional services company, Insight42 is dedicated to optimizing security, backup, DR, and resilience to protect individual rights in the digital realm.

Image: A single, glowing, holographic figure stands within a personal, transparent energy shield.
33. Rights are not granted by platforms or states; they’re protected from them.
This is the cornerstone of a free society. Our rights to privacy and property are inherent. Our professional services for optimizing security are designed to build technical safeguards that protect these rights, ensuring your systems are a fortress for your users and your business.
34. Free speech needs infrastructure, not slogans.
A truly free society requires an infrastructure of free speech: decentralized, interoperable, and censorship-resistant. This is an engineering challenge. We help clients explore and build these systems, sometimes leveraging blockchain technology to create truly immutable and censorship-resistant platforms.
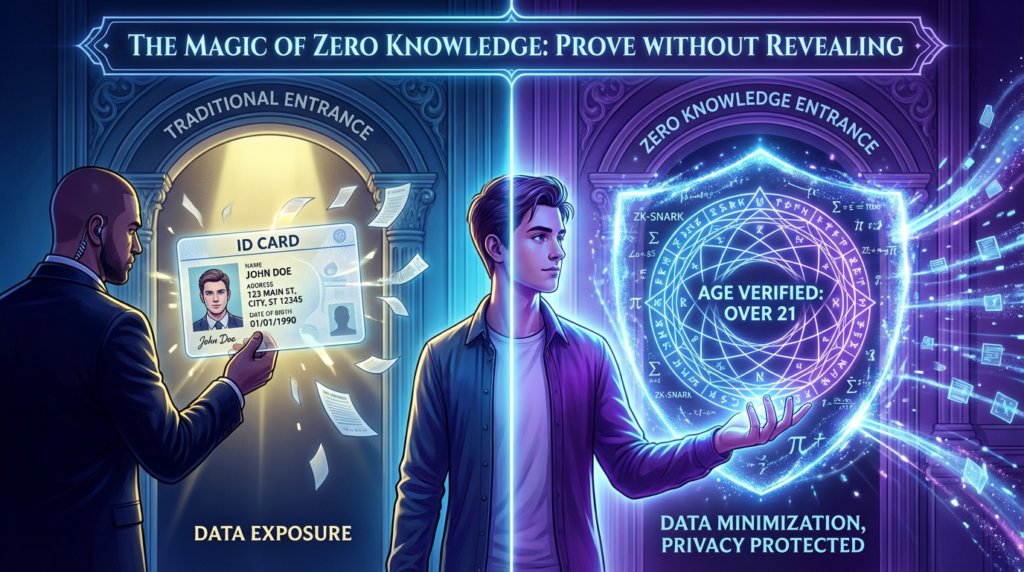
35. Identity should be user-controlled and portable.
If your identity is controlled by a platform, your speech is merely permissioned. A user-controlled, portable identity system is the foundation of a free digital society. When building mobile end-to-end applications, we prioritize decentralized identity solutions to give users control.
36. Encryption is human-rights infrastructure.
Privacy is not a luxury. Encryption is the technology that makes privacy possible. Our expertise in optimizing security includes implementing end-to-end encryption for all data, whether in transit after a cloud migration or at rest in your new data warehouse.
Competition is a Civil Liberty in Digital Markets
Competition is the freedom to choose. In the digital age, where monopolies can form rapidly, robust competition is more urgent than ever. This requires technical solutions that enable choice, a core principle of our cloud migration services.

Image: A visual representation of interoperability between digital platforms.
37. Monopolies don’t need censorship laws to shape speech; they just change algorithms.
The only effective remedy for algorithmic censorship is choice. Our professional services focus on building systems with open standards, ensuring you are never locked into a single vendor after building your cloud.
38. Interoperability is the “freedom of assembly” for software.
Interoperability is the enemy of the walled garden. When building BI, DWH, automation, data analytics, or AI platforms, we prioritize interoperability to ensure your systems can communicate and share data freely and securely.
39. Data portability is the right to emigrate.
If you cannot take your data with you, you are a hostage. A true right to data portability must be simple and enforceable. Our cloud migration services are designed to ensure your data is always portable, giving you the ultimate freedom to choose the best provider.
Europe’s Future Tasks: Security That Doesn’t Turn into Control
As Europe builds its digital future, it must not trade freedom for security. The most secure systems are often the most decentralized. This is the philosophy behind our services for optimizing security, backup, DR, and resilience.
Image: A decentralized network resiliently repelling attackers.
40. Security must be measurable and decentralized.
The only viable approach to security is a decentralized one, based on Zero Trust principles. Our security audits and implementation services help you move beyond perimeter-based thinking to a modern, measurable, and decentralized security posture for your entire infrastructure, including your mobile end-to-end applications.
41. Public digital systems should be “auditable by default.”
Transparency is the best disinfectant. Public digital systems should be designed to be auditable. For the highest level of trust and transparency, we can help you implement blockchain solutions that make your systems verifiable by design.
42. Teach sovereignty as capability: build, verify, exit, repeat.
True sovereignty is a dynamic capability. It is the ability to build your own systems, verify their integrity, and exit relationships that no longer serve your interests. Insight42 is the professional services partner that empowers you with this capability, from initial cloud migration to ongoing optimization of security and resilience.
Build a Digital Future That is Both Secure and Free
Are you ready to build a more free and sovereign digital future? At Insight42, we are your professional services partner for building secure, resilient, and decentralized digital systems.
Our expert services include:
- Optimizing Security, Backup, DR, and Resilience: We build and manage robust, end-to-end security architectures that protect your freedom and your assets.
- Blockchain: We design and implement decentralized solutions for ultimate transparency, security, and trust.
- Cloud Migration: We move you to the cloud with a strategy that ensures your sovereignty and right to exit.
- Building Your Cloud: We create custom cloud environments that are secure, resilient, and under your control.
- Mobile End-to-End Applications: We develop secure mobile applications that respect user privacy and data ownership.
- Building BI, DWH, Automation, Data Analytics & AI: We ensure your data-driven initiatives are built on a foundation of security and trust.
Contact us today for a consultation and let Insight42 help you build a digital future that is not only secure, but also free.
Hashtags:
#Cybersecurity #DigitalFreedom #DataPrivacy #Blockchain #ZeroTrust #CloudSecurity #Resilience #DR #Backup #Insight42 #DigitalTransformation #ITConsulting #ProfessionalServices #CloudMigration #MobileSecurity