Digital Sovereignty for the Public Sector
Meta Description: Sovereign Cloud Germany: What does digital sovereignty mean for public authorities? Data residency, key management, and BSI C5 compliance.
What Does Digital Sovereignty Mean?
Digital sovereignty is the ability to control one’s own IT infrastructure and data with self-determination. For the public sector, this is not a luxury but a necessity. It is about controlling citizen data, independence from individual providers, and compliance with German and European legal norms (GDPR, Schrems II).
A sovereign cloud in Germany provides the technical and organizational framework to ensure this control. It combines the innovative power of global hyperscalers (like Azure and GCP) with the strict requirements of German and European law.
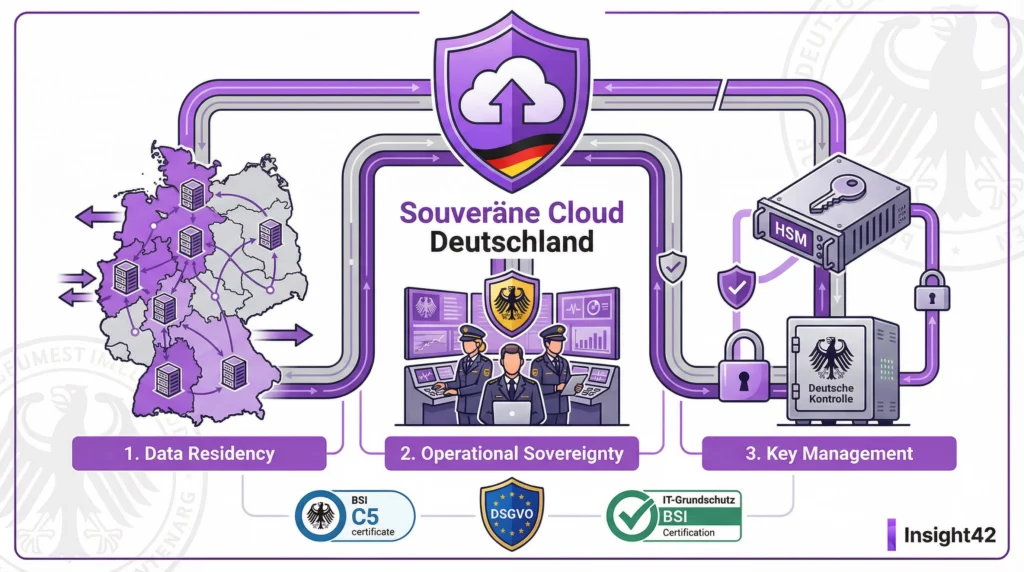
The Three Pillars of Digital Sovereignty
1. Data Residency
- What it is: The guarantee that data and metadata are stored and processed exclusively within a defined geographical area (e.g., Germany).
- Why it matters: Prevents access by foreign authorities based on laws like the US CLOUD Act. Ensures compliance with GDPR.
- Implementation: Use of cloud regions in Germany (e.g., Frankfurt, Berlin). Contractual assurances from the provider.
2. Control & Transparency
- What it is: The ability to seamlessly control and log access to data and systems, including access by the cloud provider itself.
- Why it matters: Creates trust. Enables proof of compliance (BSI C5, GDPR).
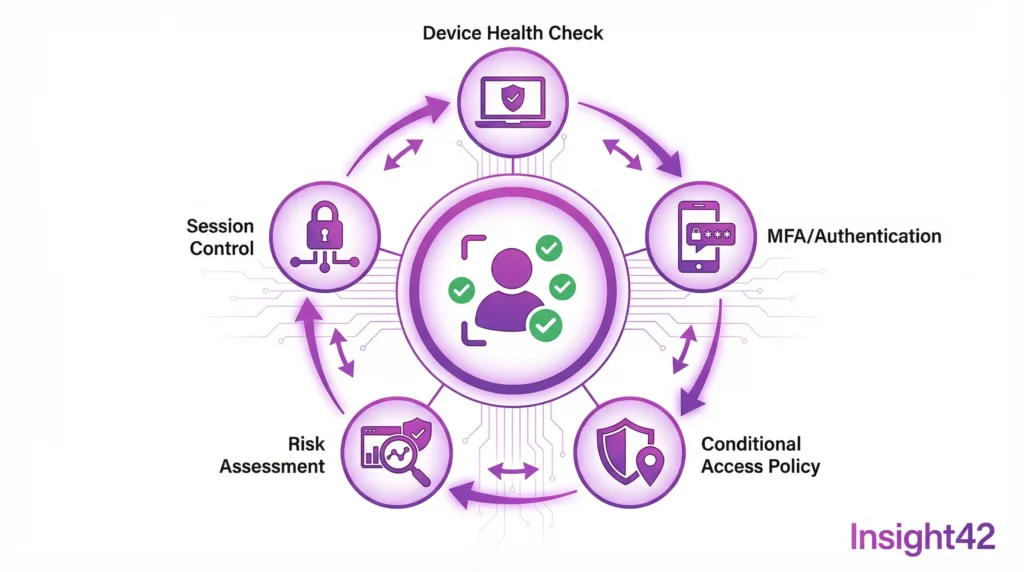
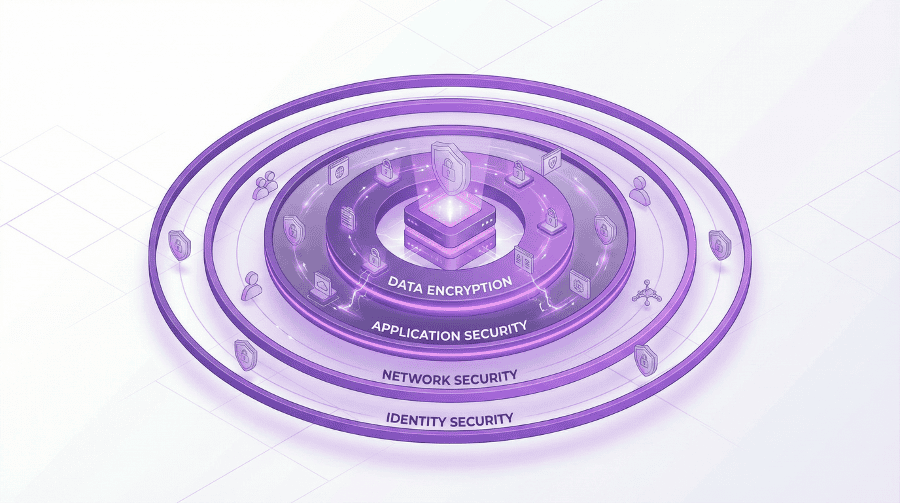
- Implementation: Strict access controls (Zero Trust, MFA), comprehensive logging, use of external control bodies (e.g., data trustees).
3. Key Management
- What it is: Control over the cryptographic keys used to encrypt data. Whoever holds the key, controls the data.
- Why it matters: It is the ultimate lever for data sovereignty. Even if a provider could access the encrypted data, they cannot read it without the key.
- Implementation: Bring Your Own Key (BYOK) or Hold Your Own Key (HYOK), where the keys remain within your own infrastructure.
Quick Checklist: Digital Sovereignty
| Pillar | Key Question | Implemented? |
| Data Residency | Is all data guaranteed to be in Germany/EU? | ☐ |
| Control | Do we have full control over all access? | ☐ |
| Transparency | Is all access logged completely? | ☐ |
| Key Management | Do we control the cryptographic keys? | ☐ |
| Compliance | Are the requirements of GDPR, BSI C5, etc., met? | ☐ |
To-Do List for a Sovereign Cloud Strategy
- Immediately: Classify the protection needs of the data.
- Week 1: Define the requirements for digital sovereignty.
- Week 2: Evaluate the market for sovereign cloud offerings (e.g., Azure, GCP, T-Systems Sovereign Cloud).
- Month 1: Establish a strategy for data residency and key management.
- Month 2: Adapt the BSI-compliant cloud security concept accordingly.
- Month 3: Start a pilot project in a sovereign cloud environment.
Sovereign Offerings from Hyperscalers
The major providers have recognized the need and offer special solutions:
- Microsoft Cloud for Sovereignty: Offers data residency, enhanced controls, and transparency. Partners like T-Systems provide additional data trustee models.
- Google Cloud Sovereign Solutions: Provides similar guarantees for data location and control, often in partnership with local providers.
These offerings are an important step but require careful examination. Cloud consulting for public authorities helps to validate the providers’ promises and find the right solution for your needs.
The Role of BSI C5 and IT Baseline Protection
Digital sovereignty and compliance go hand in hand. Being BSI C5 compliant is a basic requirement for a sovereign cloud. The controls in the C5 catalog cover many aspects of sovereignty, especially in the areas of transparency and operational security.
IT Baseline Protection consulting helps to integrate the BSI’s requirements into the cloud architecture. An ISO 27001 certification based on IT Baseline Protection demonstrates the effectiveness of the implemented measures.
Insight42: Your Guide to Digital Sovereignty
The path to a sovereign cloud is complex. We navigate you safely through the technological, legal, and organizational challenges. We know the offerings, the pitfalls, and the success factors.
We help you develop a strategy tailored to your specific protection needs—from data residency to external key management. Secure, BSI C5 compliant, and future-proof.
Take control. Contact us.
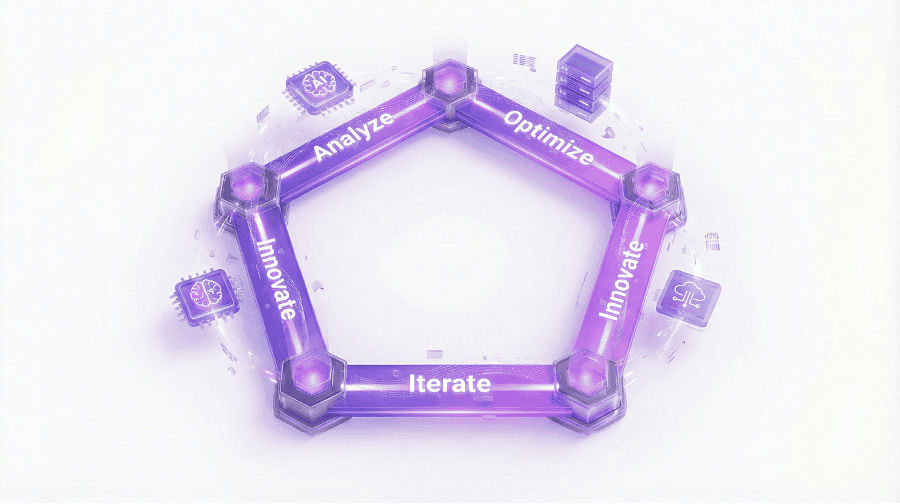
Figure: The Three Pillars of Digital Sovereignty in the Cloud
Blog Post 2: Cloud Key Management – BYOK vs. HYOK in Azure and GCP
Meta Description: Cloud Key Management: The ultimate lever for data sovereignty. A comparison of BYOK (Bring Your Own Key) and HYOK (Hold Your Own Key) in Azure and GCP.
Whoever Holds the Key, Holds the Power
Encryption is the foundation of cloud security. But who controls the keys? By default, the cloud provider does. This is convenient, but often not sufficient for sensitive government data. Because whoever controls the key can decrypt the data. This includes the provider itself and potentially foreign authorities.
The solution: Take control of your keys yourself. The two most important models for this are Bring Your Own Key (BYOK) and Hold Your Own Key (HYOK).
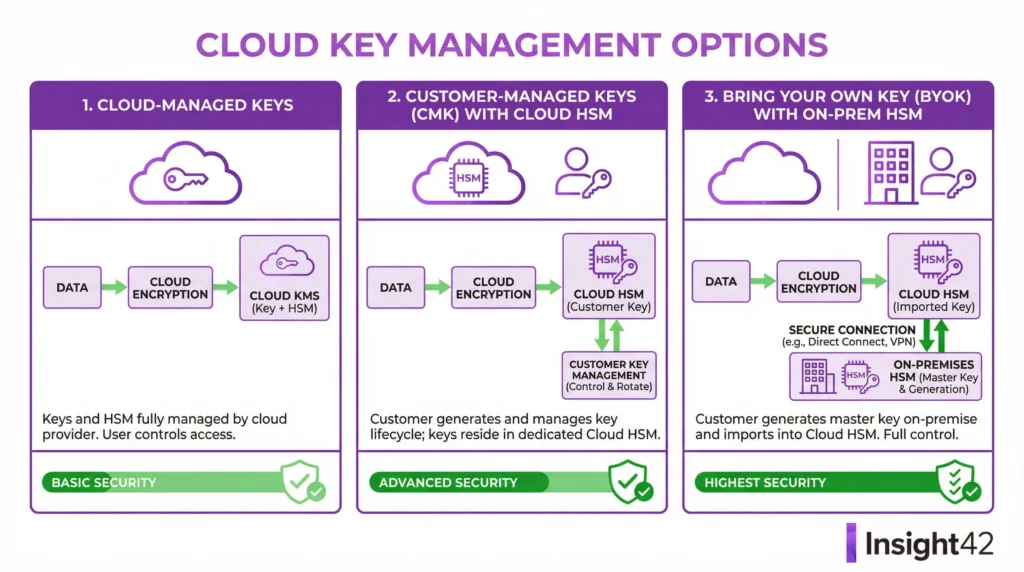
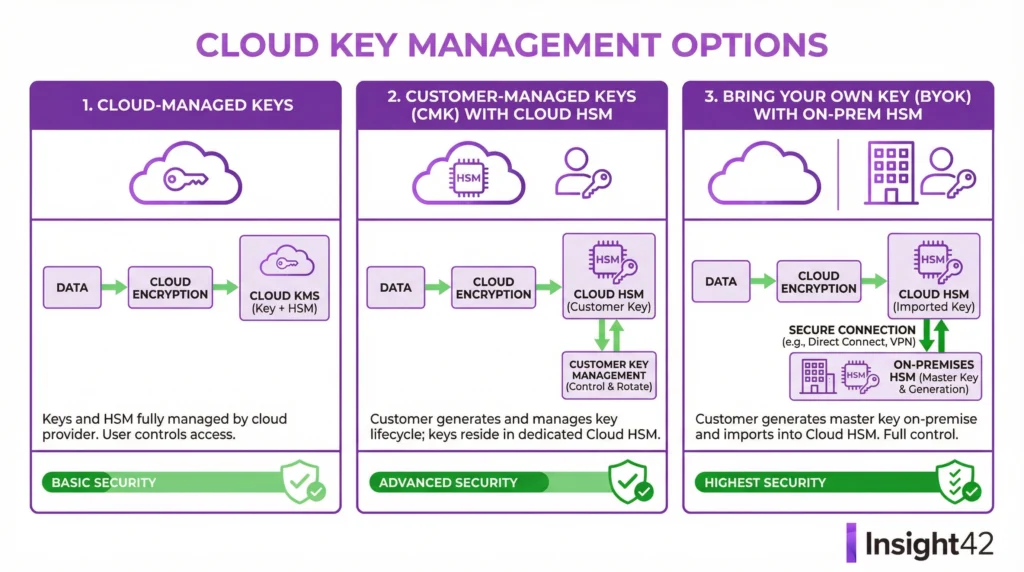
Bring Your Own Key (BYOK)
- The Principle: You create your keys in your own environment (e.g., with an on-premises Hardware Security Module – HSM) and securely import them into the cloud provider’s key management system (e.g., Azure Key Vault, GCP Cloud KMS).
- Advantages:
- Full control over the creation and lifecycle of the key.
- The key can be revoked (deleted) at any time, rendering the data unusable.
- Relatively simple integration with most cloud services.
- Disadvantages:
- The key is physically located in the provider’s cloud. Access by the provider, though unlikely, is not 100% technically impossible.
- Provider Services: Azure Key Vault (Premium Tier), GCP Cloud KMS with imported keys.
Hold Your Own Key (HYOK) / External Key Management
- The Principle: The key never leaves your own controlled environment. The cloud services send the data to be encrypted or decrypted to your external key manager. The key itself is never transferred.
- Advantages:
- Maximum control and sovereignty. The key is physically and logically separate from the cloud.
- Access by the cloud provider or third parties is technically impossible.
- Disadvantages:
- Higher complexity and potentially higher latency.
- Requires a highly available own key management infrastructure.
- Not supported by all cloud services.
- Provider Services: Azure Key Vault Managed HSM, GCP External Key Manager (EKM).
Quick Checklist: Which Model is Right?
| Criterion | BYOK | HYOK/EKM |
| Sovereignty Level | High | Very High |
| Complexity | Medium | High |
| Performance | High | Medium |
| Cost | Medium | High |
| Service Compatibility | Broad | Limited |
| Recommendation for | Standard for sensitive data | Highest protection needs (KRITIS, classified information) |
To-Do List for Sovereign Key Management
- Week 1: Analyze the protection needs of the data requiring key control.
- Week 2: Evaluate the BYOK and HYOK offerings of the cloud providers in detail.
- Month 1: Decide on a model (or a combination).
- Month 2: Create a concept for the on-premises HSM infrastructure (if necessary).
- Month 3: Configure the key management service in the cloud.
- Month 4: Define processes for key lifecycle management (creation, rotation, deletion).
Integration into the Security Architecture
External key management is not an isolated topic. It must be integrated into the overall BSI-compliant cloud security concept. It is a central measure for meeting the requirements of BSI C5, IT Baseline Protection, and GDPR.
The processes surrounding key management must be clearly defined and documented. Who can create keys? Who approves their use? What happens in an emergency? IT Baseline Protection consulting helps to design these processes robustly.
Insight42: Experts in Cloud Key Management
We help you regain control over your keys and thus your data. We analyze your needs, compare the solutions, and implement the model that is right for you.
Whether it’s BYOK with Azure Key Vault or HYOK with external HSMs – we have the expertise to technically implement your sovereign cloud strategy. Secure, compliant, and manageable.
Lock your data securely. Talk to us.
Figure: Comparison of Key Management Models BYOK and HYOK
#DigitalSovereignty #SovereignCloud #DataResidency #KeyManagement #BYOK #HYOK #CloudSecurity #PublicSector #GovTech #GDPR #SchremsII #BSIC5 #ITBaselineProtection #Azure #GCP #DataSecurity #Encryption #CloudMigration #Insight42