Wave 4: Establish Governance – Enabling Speed with Safety
As you begin to scale your cloud presence, the complexity of managing it grows exponentially. Without a strong governance framework, organizations often face a difficult choice: move fast and break things, or move slow and miss opportunities. Wave 4: Establish Governance – Enabling Speed with Safety is designed to eliminate this trade-off, allowing you to establish governance which ensures both speed and safety. It’s about creating a system of automated controls and clear policies that allow your teams to innovate with speed, while ensuring the entire environment remains secure, compliant, and cost-effective.
Effective governance is not about restricting access; it’s about providing a safe and efficient path forward, establishing governance while enabling speed and safety simultaneously. It’s the digital guardrails that keep your cloud journey on track.
Step 1: Implement Automated Guardrails
The cornerstone of modern cloud governance is automation. Instead of relying on manual reviews and approvals, you can codify your policies and enforce them automatically. These Automated Guardrails, often implemented using Infrastructure as Code (IaC) tools like Terraform or native cloud services, can:
- Prevent the creation of non-compliant resources (e.g., publicly exposed storage buckets).
- Ensure all resources are tagged correctly for cost allocation.
- Automatically remediate common security misconfigurations.
This approach, known as Governance as Code, aligns with Wave 4’s focus on enabling speed without compromising safety.
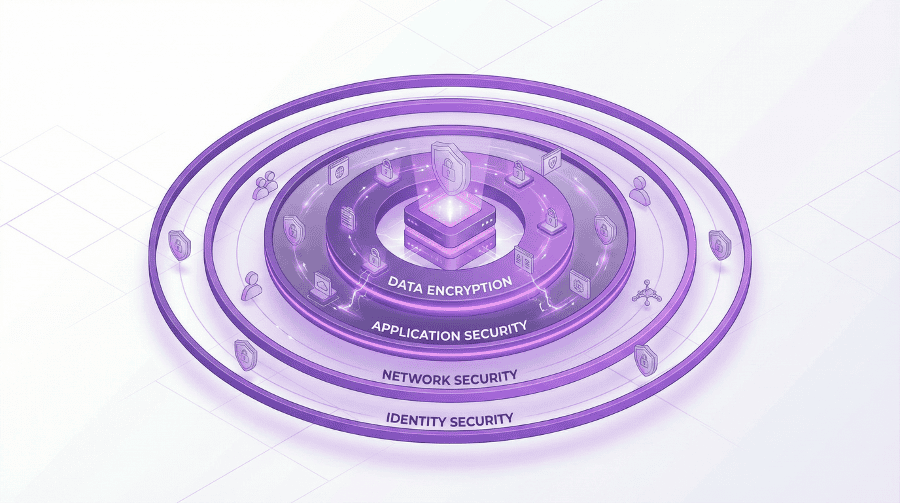
Step 2: Define and Enforce Security Policies
Your security posture is only as strong as the policies that define it. This step involves creating a comprehensive set of Cloud Security Policies that cover every layer of the environment. This is not a one-size-fits-all exercise; policies must be tailored to your organization’s risk appetite and regulatory requirements. Key areas to cover include:
- Identity and Access Management (IAM): Who can access what, and under what conditions?
- Data Encryption: Ensuring data is encrypted both at rest and in transit.
- Network Security: Defining firewall rules, network segmentation, and threat detection.
- Incident Response: A clear plan for how to respond to a security event.
These policies should be centrally managed and automatically enforced by the guardrails you’ve built, enabling the governance wave to drive both speed and safety without missing opportunities.
Step 3: Establish Financial Governance (FinOps)
Cloud costs can spiral out of control without disciplined financial management. FinOps, or Cloud Financial Operations, is the practice of bringing financial accountability to the variable spend model of the cloud. This involves:
- Cost Visibility: Creating dashboards that give teams real-time insight into their cloud spend.
- Cost Allocation: Using a robust tagging strategy to allocate costs back to the appropriate business units or projects.
- Cost Optimization: Continuously identifying and eliminating waste, such as idle resources or oversized instances.
A mature FinOps practice ensures financial governance that maximizes business value while enabling speed and ensuring safety.
Step 4: Automate Compliance and Auditing
For many organizations, especially those in regulated industries, proving compliance is a constant challenge. The cloud offers the opportunity to automate much of this process. By using specialized tools, you can continuously monitor your environment against hundreds of compliance controls (like CIS, NIST, PCI DSS, or HIPAA). This Automated Compliance Auditing provides real-time visibility into your compliance posture and dramatically simplifies the audit process, turning a weeks-long manual effort into an on-demand report.
By the end of Wave 4, you have built a well-governed cloud factory. You have the systems in place to manage risk, control costs, and ensure compliance without slowing down your developers. This robust governance framework naturally establishes speed with safety, providing confidence in cloud adoption.
#CloudGovernance #FinOps #CloudSecurity #ComplianceAutomation #IaC #CostOptimization #FinancialOperations #SecurityPolicies #GovernanceAsCode #ComplianceAutomation #CloudGuardrails #IAMPolicies #CostAllocation #RiskManagement #EnterpriseGovernance