
Stop Git Impersonation, Strengthen Supply Chain Security, Meet US & EU Compliance
If you build software professionally, you don’t just need secure code—you need verifiable proof of who changed it and whether it was altered before release. Code Signing & Signed Commits play a crucial role in preventing Git impersonation and meeting US/EU compliance requirements such as NIS2, GDPR, and CRA. That’s why code signing (including Git signed commits) has become a baseline control for software supply chain security, DevSecOps, and compliance.
It also directly addresses a common risk: a developer (or attacker) committing code while pretending to be someone else. With unsigned commits, names and emails can be faked. With signed commits, identity becomes cryptographically verifiable.
This matters even more if you operate in the US and Europe, where cybersecurity requirements increasingly expect strong controls—and where the EU, in particular, attaches explicit, high penalties for non-compliance (NIS2, GDPR, and the Cyber Resilience Act). (EUR-Lex)

What is “code signing” (and what customers actually mean by it)?
In industry conversations, code signing usually means a chain of trust across your entire delivery pipeline:
- Signed commits (Git commit signing): proves the author/committer identity for each change
- Signed tags / signed releases: proves a release point (e.g.,
v2.7.0) wasn’t forged - Signed build artifacts: proves your binaries, containers, and packages weren’t tampered with
- Signed provenance / attestations: proves what source + CI/CD pipeline produced the artifact (a growing expectation in supply chain security programs)
The goal is simple: integrity + identity + traceability from developer laptop to production.
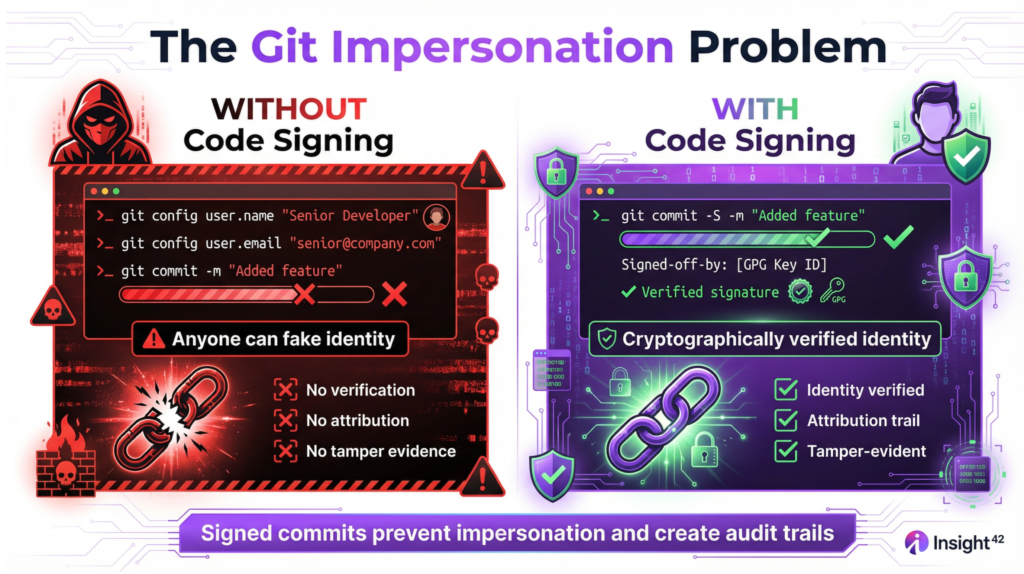
Why signed commits prevent “commit impersonation”
Without signing, Git identity is just text. Anyone can set an author name/email to match a colleague and push code that looks legitimate.
Signed commits add a cryptographic signature that platforms can verify. When you enforce signed commits (especially on protected branches):
- fake author names don’t pass verification
- only commits signed by trusted keys are accepted
- auditors and incident responders get a reliable attribution trail
In other words: Git commit signing is one of the cleanest ways to prevent developers (or attackers) from committing as someone else.
Code Signing = Better Security + Cleaner Audits
Customers in regulated industries (finance, critical infrastructure, healthcare, manufacturing, government vendors) frequently search for:
- “software supply chain security”
- “CI/CD security controls”
- “secure SDLC evidence”
- “audit trail for code changes”
Code signing helps because it creates durable evidence for:
- change control (who changed what)
- integrity (tamper-evidence)
- accountability (strong attribution)
- faster incident response and forensics
That’s why code signing is often positioned as a compliance accelerator: it reduces the cost and friction of proving good practices.
US Compliance View: Why Code Signing Supports Federal and Enterprise Security Requirements
In the US, the big push is secure software development and software supply chain assurance—especially for vendors selling into government and regulated sectors.
Executive Order 14028 + software attestations
Executive Order 14028 drove major follow-on guidance around supply chain security and secure software development expectations. (NIST)
OMB guidance (including updates like M-23-16) establishes timelines and expectations for collecting secure software development attestations from software producers. (The White House)
Procurement artifacts like the GSA secure software development attestation reflect this direction in practice. (gsa.gov)
NIST SSDF (SP 800-218) as the common language
Many organizations align their secure SDLC programs to the NIST Secure Software Development Framework (SSDF). (csrc.nist.gov)
Where code signing fits: it’s a practical control that supports identity, integrity, and traceability—exactly the kinds of things customers and auditors ask for when validating secure development practices.
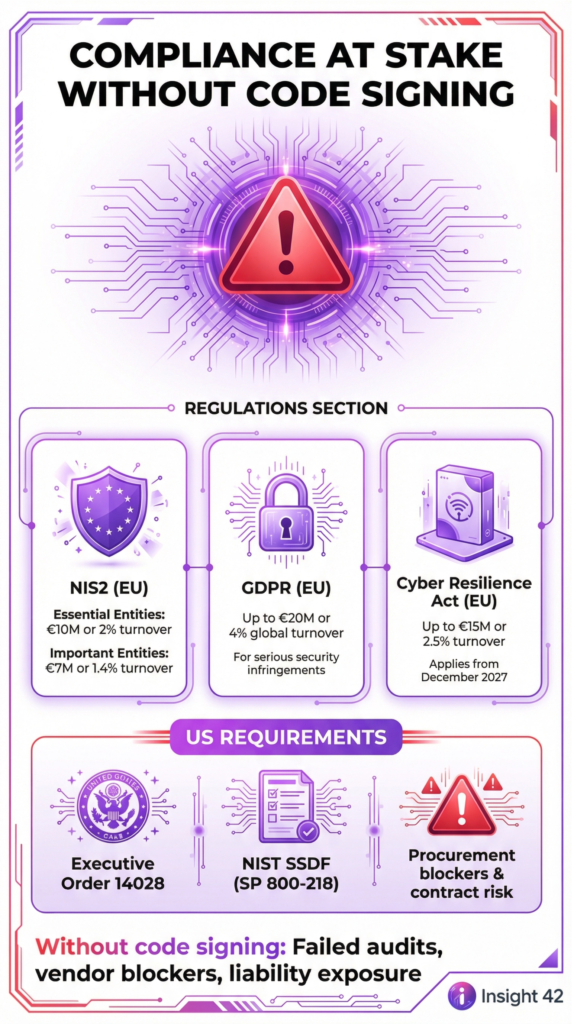
(In the US, the “penalty” is often commercial: failed vendor security reviews, procurement blockers, contract risk, and higher liability after an incident—especially if your controls can’t be evidenced.)
EU Compliance View: NIS2, GDPR, and the Cyber Resilience Act (CRA) Penalties
Europe is where penalties become very concrete—and where customers increasingly ask vendors about NIS2 compliance, GDPR security, and Cyber Resilience Act compliance.
NIS2 penalties (explicit fines)
NIS2 includes an administrative fine framework that can reach:
- Essential entities: up to €10,000,000 or 2% of worldwide annual turnover (whichever is higher)
- Important entities: up to €7,000,000 or 1.4% of worldwide annual turnover (whichever is higher) (EUR-Lex)
Why code signing matters for NIS2 readiness: it supports strong controls around integrity, accountability, and change management—key building blocks for cybersecurity governance in professional environments.
GDPR penalties (security failures can get expensive fast)
GDPR allows administrative fines up to €20,000,000 or 4% of global annual turnover (whichever is higher) for certain serious infringements. (GDPR)
Code signing doesn’t “solve GDPR,” but it reduces the risk of supply-chain compromise and improves your ability to demonstrate security controls and traceability after an incident.
Cyber Resilience Act (CRA) penalties + timelines
The CRA (Regulation (EU) 2024/2847) introduces horizontal cybersecurity requirements for products with digital elements. Its penalty article states that certain non-compliance can be fined up to:
- €15,000,000 or 2.5% worldwide annual turnover (whichever is higher), and other tiers including
- €10,000,000 or 2%, and €5,000,000 or 1% depending on the type of breach. (EUR-Lex)
Timing also matters: the CRA applies from 11 December 2027, with earlier dates for specific obligations (e.g., some reporting obligations from 11 September 2026 and some provisions from 11 June 2026). (EUR-Lex)
For vendors, this translates into a customer question you should expect to hear more often:
“How do you prove the integrity and origin of what you ship?”
Your best answer includes code signing + signed releases + signed artifacts + verifiable provenance.
Implementation Checklist: Code Signing Best Practices (Practical + Auditable)
If you want code signing that actually holds up in audits and real incidents, implement it as a system—not a developer “nice-to-have”.
1) Enforce Git signed commits
- Require signed commits on protected branches (
main,release/*) - Block merges if commits are not verified
- Require signed tags for releases
2) Secure developer signing keys
- Prefer hardware-backed keys (or secure enclaves)
- Require MFA/SSO on developer accounts
- Rotate keys and remove trust when people change roles or leave
3) Sign what you ship (artifact signing)
- Sign containers, packages, and binaries
- Verify signatures in CI/CD and at deploy time
4) Add provenance (supply chain proof)
- Produce build attestations/provenance so you can prove which pipeline built which artifact from which source
FAQ (high-intent keywords customers search)
Is Git commit signing the same as code signing?
Git commit signing proves identity and integrity at the source-control level. Code signing often also includes release and artifact signing for what you ship.
Does signed commits stop a compromised developer laptop?
It helps with attribution and tamper-evidence, but you still need endpoint security, key protection, least privilege, reviews, and CI/CD hardening.
What’s the business value?
Less impersonation risk, stronger software supply chain security, faster audits, clearer incident response, and a better compliance posture for US and EU customers.
Takeaway
If you sell software into regulated or security-sensitive markets, code signing and signed commits are no longer optional. They directly prevent commit impersonation, strengthen software supply chain security, and support compliance conversations—especially in the EU where NIS2, GDPR, and CRA penalties can be severe. (EUR-Lex)
If you want, I can also provide:
- an SEO-focused FAQ expansion (10–15 more questions),
- a one-page “Code Signing Policy” template,
- or platform-specific enforcement steps (GitHub / GitLab / Azure DevOps / Bitbucket) written in a customer-friendly way.
#CodeSigning #SignedCommits #GitSecurity #SoftwareSupplyChain #SupplyChainSecurity #DevSecOps #SecureSDLC #CICDSecurity #NIS2 #GDPR #CyberResilienceAct #Compliance #RegTech #RiskManagement #CybersecurityGovernance #SoftwareIntegrity #CodeIntegrity #IdentitySecurity #NonRepudiation #ZeroTrust #SecurityControls #ChangeManagement #GitHubSecurity #GitLabSecurity #SBOM #SLSA #SoftwareProvenance #ArtifactSigning #ReleaseSigning #EnterpriseSecurity #CloudSecurity #SecurityLeadership #CISO #SecurityEngineering #ProductSecurity #SecurityCompliance